In a small town in Alaska, a sophisticated cyber attack nearly wiped out the Matanuska-Susitna (Mat-Su) Borough network servers with a virus cocktail of ransomware, a trojan horse, time bomb, Cryptolocker and dead man’s switch, according to reports by BleepingComputer and BBC. This attack forced the town’s businesses to dust off old typewriters and conduct business by hand until IT experts were able to get back online.
While the use of machines that click clack is unsustainable in the digital world, the Mat-Su attack is just one example of the type of criminal activity happening in the public sector that keeps cyber warriors on their toes.
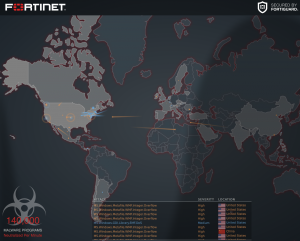
According to Statista, government agencies are at the top of the list for cyber attacks, which involve “non-state actors, such as terrorist groups, political or ideological extremists groups, transitional criminal organizations and hacktivists,” who intend to cause destruction or mayhem.
Between 2014 and Q1 2018, the U.S. government and military reported 350 million breaches to their systems, according to Statista. And in 2015, the government dealt with the largest global data online breach to its U.S. voter database.

Penetration by foreign governments is a real threat and an on-going battle for our nation's online warriors.
Dr. Greg Miles, Program Champion of Cyber Studies at the University of Advancing Technology, principal of Peak Security and former Black Hat teacher, said the most prevalent foreign countries initiating attacks include Russia, China, North Korea and Brazil.
“Their goal is pure disruption with the intent to cause fear, uncertainty and doubt in U.S. organizations,” Miles said.
Russia has been on the radar for some time, especially with the ongoing federal investigation into the 2016 elections. The Russian hacker group, referred to as “Fancy Bear,” hacked the Democratic National Committee computers and exposed information about political candidates. The CIA determined that Russia’s motive was to assist Donald Trump to win the election instead of “undermine confidence in the U.S. electoral system,” according to the Washington Post.
Recently, the Department of Homeland Security (DHS), FBI and UK officials issued a joint warning about Russian attacks to everyday equipment such as routers, switches, firewalls and our power grid system.

“These hackers want to create a level of chaos where people can’t conduct business in a regular manner and target critical infrastructures that affects people and the ability of governments to keep control of our citizens,” Miles said.
The top two concerns from these agencies include the ability to “access data and intellectual property, allowing them to spy on companies and individuals and steal not only their secrets but the data that they use to run their businesses. The second, is that the Russians could be setting up backdoors that would allow them to take down critical infrastructure such as banking, energy and manufacturing as a precursor to actual physical war,” as reported by USA Today.
With increasing threats to our country’s defense systems, the Department of Homeland Security (DHS) developed the Cyber Incident Response center that “share threat information with private companies [and] identify the country’s digital ‘crown jewels’ that may be especially vulnerable,” as reported by Fifth Domain.
“If hackers can get defense designs, they will either build defense systems themselves or find vulnerabilities to disrupt our defense systems,” Miles said.
The House passed legislation for the Cyber Incident Response center authorizing their warriors to hunt down cyber criminals and “help owners and operators of critical infrastructure respond to cyber attacks as well as provide strategies for mitigating cyber security risks. The bill would also allow the Secretary of Homeland Security to add cyber security specialists from the private sector to the response teams,” according to The Hill.
With the need for more online warriors, the public and private sector are investing in more talent and technology. Within Arizona, there are over 40 cyber security companies in different stages and currently over 10,000 job postings within the industry, according to cyberseek.org. And “for the 2019 fiscal year, the U.S. federal government has budgeted $45.8 billion for federal IT spending,” according to Statista.
READ: Arizona Cyber Security Sector Needs More People Faster
For those looking to fight in the nation’s online war, picking the right educational program can make you more attractive to government agencies.
The National Center of Academic Excellence (CAE) is an accredited cyber security program sponsored by the DHS and National Security Agency (NSA) given to colleges for their alignment to their “specific cyber security-related knowledge units vital to securing our nation’s information systems and validated by top subject matter experts in the field.”
For 22 years, University of Advancing Technology (UAT) has graduated cyber warriors from one of the longest running CAE designated programs in the U.S. At UAT, students can build their skills and obtain a cyber security degree in a shorter amount of time than at a state school and enter the workforce 2.5 years earlier on average with a higher level position and salary.
UAT takes an applicable approach to cyber education to prepare students for battle and make an impact. In UAT’s cyber security program, students engage in real-world activities, develop and redefine ethical hacking skills in UAT’s Cyber Warfare Range, which is equipped with 16 FRED machines (funded by a D.O.D grant) and experiment with tools in an isolated environment.
 FRED Forensic Workstations
FRED Forensic Workstations
UAT students are pushed to think out-of-the-box, develop innovative ways to combat attacks and demonstrate their cyber warrior abilities. To support a student’s growth, the Cyber Advisory Board brings in alumni to help mentor students for potential cyber intern opportunities with government agencies.
Aside from education and training, there are important qualities that make up a strong cyber warrior.
“You must have the desire, passion, need to learn and protect, and the ability to think outside the box. These attackers are going to generally be one step ahead of you and you have to think a lot like an attacker in order to put the right defenses in place for whatever organization you work for,” Miles said.
Learn more about UAT’s cyber security program HERE.




Comment