Commentary: Dr. Natasha Vita-More
Professor, Undergraduate and Graduate Programs
University of Advancing Technology
On Saturday, February 15, UAT’s Cybersecurity team participated in the Western Regional Cyber Defense Competition. UAT’s team was made up of 8 students, all taking on different roles as team members.

To set up for the competition, I arrived at 9:00am and ran a check of the team members and their titles by checking off the list provided to me by Dr. Brandon R. Brown, the Director of WRCCDC. To be on the safe side, and just in case we came in with a high-ranking, I checked off each student’s name and requested to view each team member’s ID. Below is my check off list:
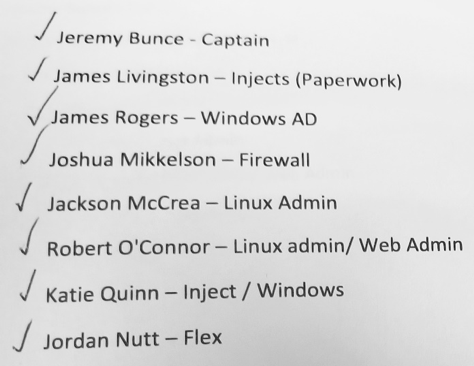
Team Captain Jeremy Bunce immediately went into action, assessing tasks, team members’ computer locations, and getting the team ready for the competition’s 10:00 AM start time. All competing teams are referred to as the Green Teams. During the competition they are performing tasks for vulnerabilities testing.
Student Teams Take on Real-World Scenarios:
You have just been hired as the network and security administrators at a small company and will be taking administrative control of all information systems. You know very little about the network, what security level has been maintained, or what software has been installed. You have one hour to familiarize yourself with the network and systems and to begin the security updates and patches before the red team starts actively attacking your company, you also have to keep up with the needs of the business and user demands while maintaining service level agreements for all critical Internet services.
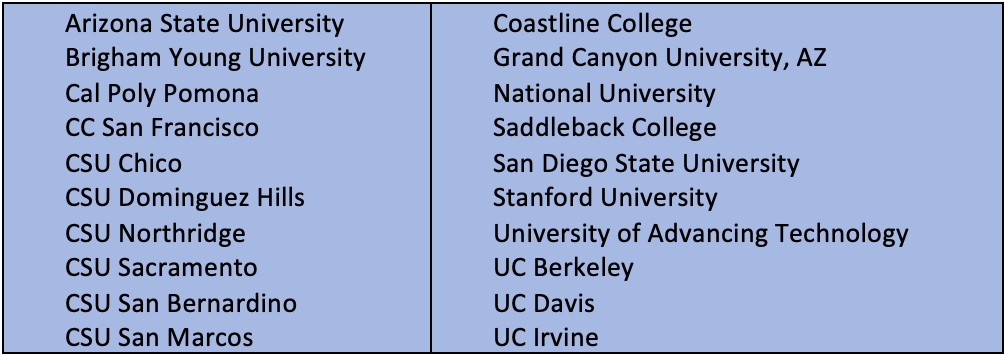
Blue Team University Participants:
Because this competition covered the West Regional area, there were 21 universities participating (in alphabetical order). Each of these university cyber teams were competing Blue Teams.
The Blue team's role was to are watch out for any vulnerabilities and hacking from their opposition, the “Red Team”. The Red Team was comprised of computers based in California. The Red Team established numerous handicaps that students had to cover come. Their aim is to simulate external hackers and attempt to gain unauthorized access to competition Blue teams’ systems.
On two separate occasions the Red Team’s servers had a breakdown in the system lasting 30 minutes each. While on standby for the computers to get back online, UAT’s team remained claim and focused.
Students worked as a team. I was delighted at the comradery and lack of egos! They helped each other, while maintaining their individual roles. At 5:10, there were two unfinished tasks for them to resolve and by 5:20 all tasks were completed, with 10 seconds left! From my observation, UAT’s team felt confident and eagerly awaiting the competition results. There was tremendous excitement and a high level of relief!
Competition Scoring
The WRCCDC wrapped up and its officials examined every inject, red team report, blue team incident report, and the carefully inspected the service scoring engine and database. Their aim was to be completely fair and transparent to make sure that no team had an advantage over another team. The teams that are advancing to the finals are listed below in order of highest scores to lower scores:
Scores
- University of Advancing Technology (UAT)
- Stanford University
- Cal Poly Pomona
- UC Irvine
- UC Berkeley
- UC Davis
- Sacramento State
- City College of San Francisco





Comment