Parents and students will be spending more time online and connected to other students, educators, and employers in the coming months. This new normal poses special challenges and can feel daunting. However, by being vigilant, paying attention to the details, and communicating with your child about privacy and personal safety, you should find this transition to be pleasant and rewarding.

1. Talk to your children about some of the dangers posed by individuals online who may want to cause them harm. Younger children should be reminded that we do not communicate with strangers or get into cars with people we do not know and so we should understand that just because someone has a social media account or an email address does not necessarily mean they are who you think they are.
2. Do not click on links that are unsolicited. Email and social media based attacks are very popular because they are effective.
3. Use an adblocker on your browser. Adblock Plus and Ublock Origin are two potential candidates that can be used on Firefox or Chrome.
4. Children that do not need all of the features of a full laptop or desktop may be better served by using web applications on a device like a Chromebook. Work with your educational institution to find out if this is a viable alternative.
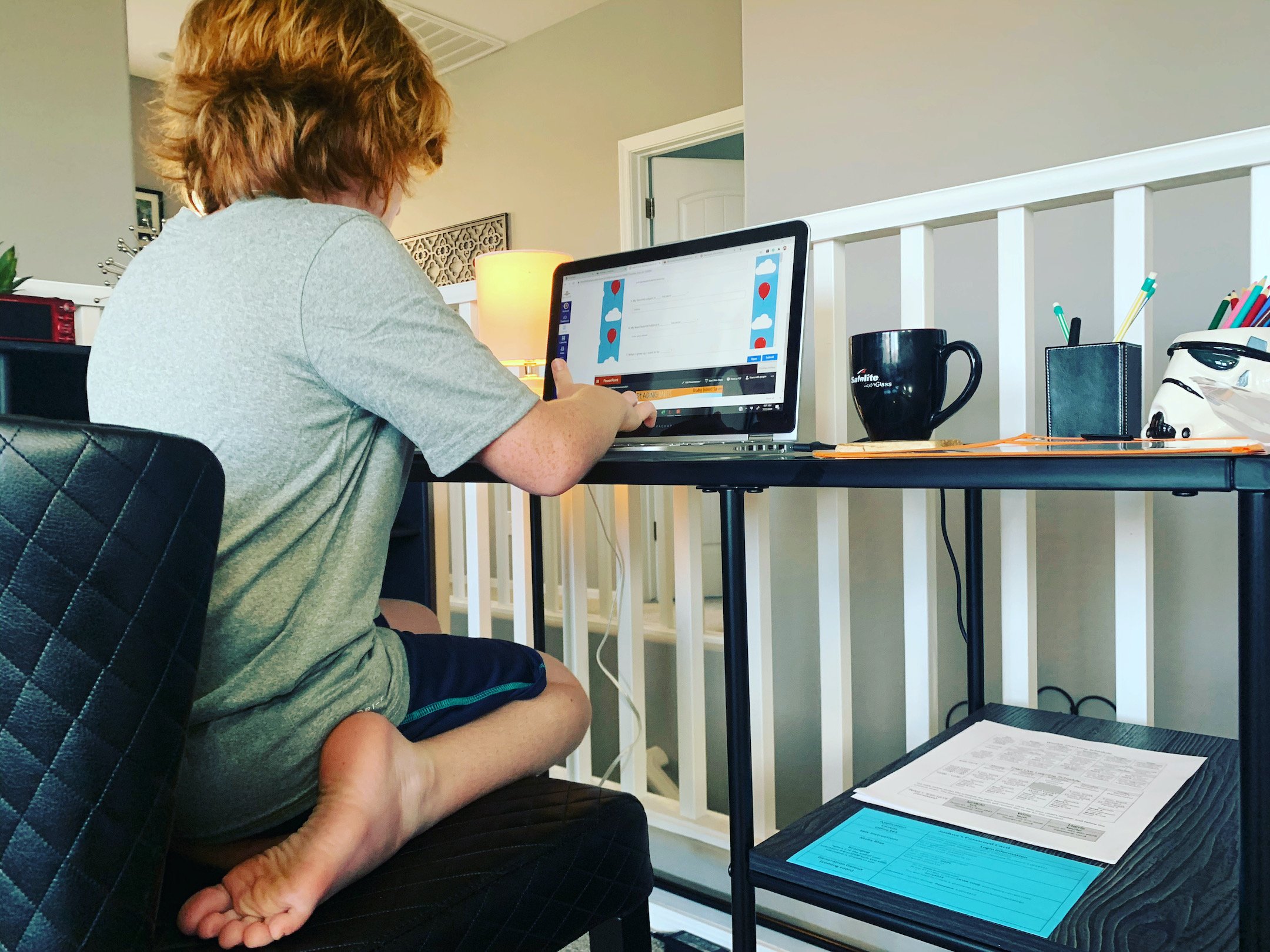
5. Use the available parental controls for your device. Windows 10, Apple Macintosh, and Android based devices have built in parental controls that can be used to control when the device is used, where individuals can go on the internet, and to audit some of the actions taken by the youngster.
6. Take an interest in your child’s social media. This may mean setting firm rules on who they can communicate or connect with. Make sure you have access to the account used by the child and that you know what email address was used to register the account and the user name used by the student. You may need to be able to provide this information to law enforcement at a later date.

7. Be cautious of individuals posing as officials from law enforcement, the government, or your school. These are common scams. Your local law enforcement is not going to contact you by phone or email about taxes, tickets, or behavior issues related to your children.
8. Verify and then trust. Do not install applications or tools provided by others or offered unsolicited. Use official methods for acquiring software. Warn children about the dangers potentially posed by piracy as threat actors often add dangerous code to cracked or stolen software.
9. Beware of phone scams offering technical support. Microsoft, Apple, and others will never contact you by phone offering support for your system or warnings about vulnerable software. Microsoft does not contact users about virus infections.
10. If you believe someone may be trying to scam you, do not hesitate to contact your local law enforcement and ask to speak to an investigator about your issue. The safety of you and your children both online as well as off is the number one priority of your local law enforcement.
Students must now acclimate to the new normal of online education. This means parents need to understand the challenges and dangers posed by an always connected class room. If parents follow these few simple rules, speak to their children about personal safety and security, and employ the technology available to them, they can have a healthier, safer, and more pleasant semester.

UAT’s cyber security degree programs and cyber security lab are recognized by industry and government entities alike for their ability to help generate the future innovators of the cyber security industry. We focus on creating true leaders who will have mastery in ethical hacking and uphold the highest industry standard of integrity in our quickly evolving world of cyber security tech and online security.
Visit https://www.uat.edu/cyber-security-degrees or email admissions@uat.edu for more information.





Comment